Feb 13, 2026
SOC 1 and SOC 2 Compliance: The Difference That Drives Decisions

By Fraxtional LLC

Summarize the blog with AI
You’ve likely seen it: one executive pushing for SOC compliance because customers demand it, another questioning the cost. While SOC reports are now standard in enterprise and sponsor bank deals, the hidden risk is audit surprises that delay deals, distort risk decisions, and erode credibility when it matters most.
In the digital services, voluntary SOC examinations are core risk assessments with measurable market impact: in one systematic accounting study of voluntary SOC audits, nearly 29% of S&P 500 firms reported undergoing these audits. This highlights their material role in audit-related fees and control evaluations.
As a startup founder, COO, compliance lead, or investor evaluating counterparties, you need clarity, not just checkboxes. In this blog, we will explain what SOC 1 and SOC 2 compliance actually measure, their differences, when you need each, and how to interpret findings from real audits.
Key Takeaways
- SOC 1 focuses on controls that impact financial reporting, while SOC 2 evaluates security, availability, and operational risk that buyers and partners care about.
- Type I reports assess control design at a point in time, but Type II reports prove controls actually worked over a period, which carries far more weight in enterprise and bank decisions.
- The right SOC report depends on how your product affects customer finances, data, and operations, and in many fintech and SaaS cases, both SOC 1 and SOC 2 are required.
- A clean SOC opinion does not mean low risk; scope boundaries, CUECs, and exceptions determine how much assurance the report truly provides.
- Fraxtional helps organizations scope, prepare, and interpret SOC audits strategically so compliance supports deals, diligence, and long-term trust rather than slowing them down.
What Problem Do SOC 1 and SOC 2 Compliance Reports Actually Solve?
In fast-moving markets, the “promise of compliance” often masks a deeper issue: buyers and investors still don’t have a reliable way to validate a vendor’s internal controls before deals are signed.
You can have hundreds of pages of policies, but without independent verification, your counterparties may delay procurement, tighten contract terms, or refuse to proceed altogether, all because they can’t assess real control effectiveness.
Below are the core problems SOC reports were designed to solve for operators and investors:
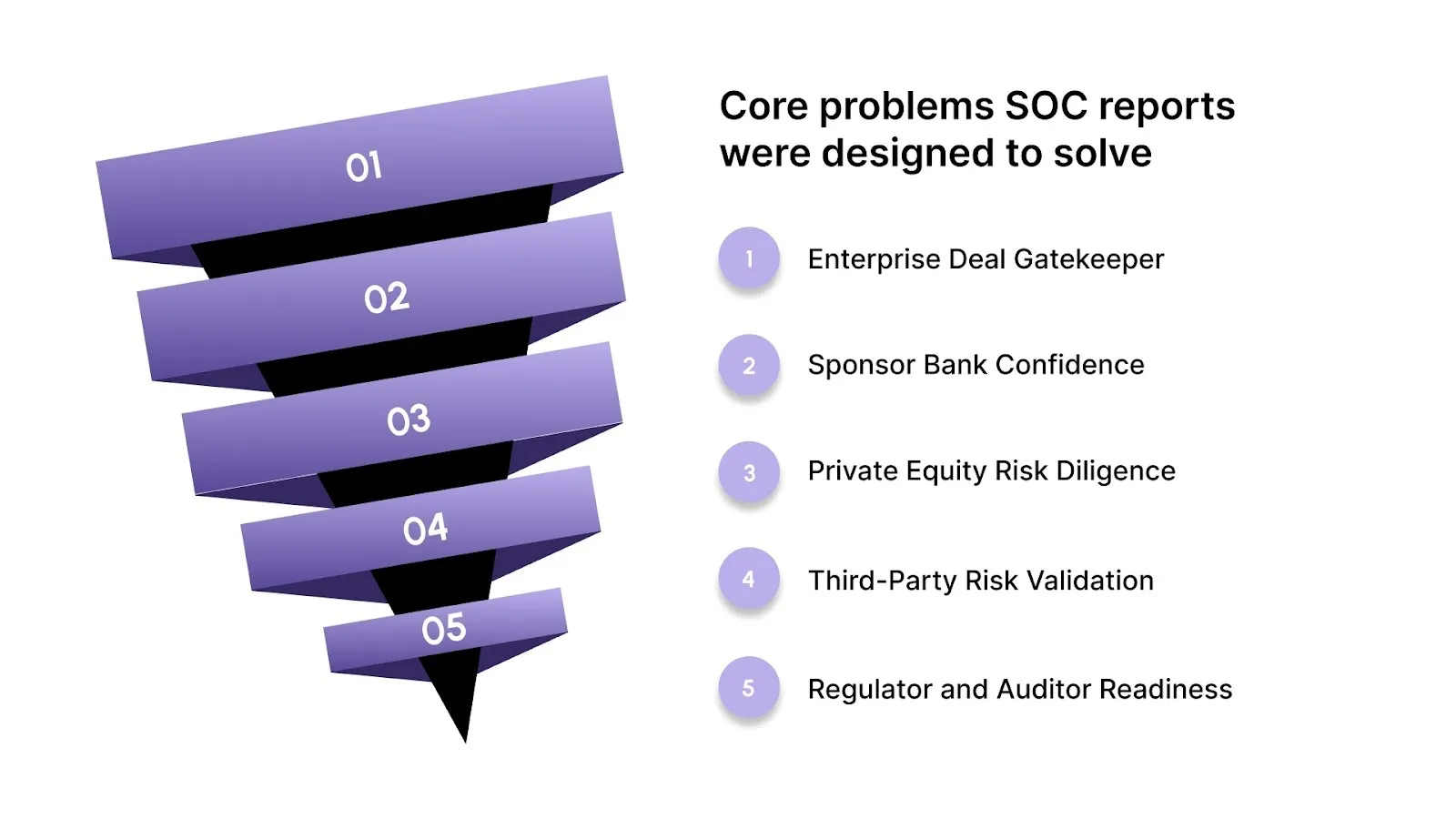
- Enterprise Deal Gatekeeper: SOC reports provide independent assurance of control environments that buyers require before advancing high-value contracts in regulated industries.
- Sponsor Bank Confidence: Banks and sponsor partners treat SOC reports as tangible evidence that controls are documented and verified by accredited auditors, not just claimed in slide decks.
- Private Equity Risk Diligence: PE firms use SOC documentation to identify gaps early in compliance and control narratives rather than after term sheets are signed.
- Third-Party Risk Validation: Instead of sifting through endless questionnaires, SOC reports enable risk and vendor management teams to evaluate control design and operation with standardized criteria.
- Regulator and Auditor Readiness: SOC examinations reduce back-and-forth with external auditors by providing trusted audit evidence rather than self-attested responses.
Also Read: Information Security Policies: Importance, Elements, and Key Questions
Once you understand the problems SOC reports are meant to solve, the next step is knowing which report applies to your business, starting with SOC 1.
What Is SOC 1 Compliance and When Does It Matter?
SOC 1 is the framework leaders use to eliminate that uncertainty by independently validating financial reporting controls, so you don’t end up in endless audit cycles or miss key enterprise deals.
Below are the critical aspects of SOC 1 that matter most to you as a founder, compliance leader, risk executive, or investor:
- Internal Control Over Financial Reporting (ICFR) Relevance: SOC 1 evaluates a service organization’s controls that directly impact a customer’s financial reporting processes, ensuring accuracy, completeness, and reliability.
- Financial Audit Dependency: External auditors rely on SOC 1 reports to assess your service provider controls instead of running their own costly alternative procedures.
- High-Impact Use Cases: SOC 1 is most relevant when your services affect payroll, transaction processing, billing, loan servicing, or financial systems that feed into client ledgers.
- Primary Stakeholder Audience: The key users of SOC 1 are customer auditors, finance teams, and audit committees, not general risk teams, because the focus is on financial statement reliability.
- Audit Evidence Value: A SOC 1 report gives you independent evidence of control design and operation, reducing redundant audit requests and improving negotiation understanding.
While SOC 1 focuses on financial reporting risk, many buyers are equally concerned with how well your operations and data are protected, which is where SOC 2 comes in.
What Is SOC 2 Compliance and Why Do Buyers Expect It?

In high-trust industries, purchasers and partners increasingly demand independent assurance that your internal controls actually function the way you claim. This expectation has transformed SOC 2 from a technical audit into a commercial and risk management asset that buyers routinely require.
Below are the core reasons SOC 2 compliance matters to enterprise buyers, sponsor banks, and private equity investors:
- Trust Services Criteria Assurance: SOC 2 evaluates controls against the AICPA’s five Trust Services Criteria, Security, Availability, Processing Integrity, Confidentiality, and Privacy, providing standardized evidence of control maturity.
- Vendor Risk Reduction in Procurement: Enterprises treat SOC 2 reports as foundational assurance supporting vendor risk decisions and procurement approvals, reducing the need for long security questionnaires and bespoke evidence requests.
- Buyer-Driven Expectation, Not Regulation: Unlike regulatory mandates, SOC 2 demand comes from contracts and partnerships: many buyers won’t proceed without it because it provides a common evidence baseline they trust.
- Faster Contracting and Approval Cycles: A verified SOC 2 report can significantly shorten enterprise sales cycles by giving legal and risk teams the independent audit evidence they require early in negotiations.
- Confidence for Financial and Strategic Backers: Banks, investors, and diligence teams view SOC 2 compliance as a practical proxy for operational resilience and security discipline, critical when evaluating financial exposure or integration risk.
Understanding why buyers expect SOC 2 is easier once you see how it differs in scope, audience, and risk focus from SOC 1.
SOC 1 vs SOC 2: 7 Key Differences Decision Makers Should Know
Understanding the practical impact of SOC 1 and SOC 2 compliance helps you make clearer risk decisions, faster procurement cycles, and stronger stakeholder confidence without relying on generic compliance checkboxes.
Below is a direct comparison highlighting the factors that matter most to enterprise buyers, sponsor banks, PE investors, and compliance leaders.
Also Read: What Is a Data Governance Policy? A Practical Guide for Regulated Teams
The distinctions become clearer once you examine the control areas and criteria auditors evaluate under each report.
What Controls and Criteria Do SOC 1 and SOC 2 Compliance Evaluate?

To make smart decisions about your audit strategy, you need a clear picture of what’s actually tested. Below are the key audit control areas for each:
1. SOC 1 Controls and ICFR Alignment
For SOC 1, auditors evaluate controls that meaningfully influence your clients’ financial reporting.
Here are the key SOC 1 control areas:
- Transaction Processing Accuracy: Controls ensuring financial transactions are recorded correctly to support accurate reporting.
- Authorization and Approvals: Mechanisms verifying that transactions are approved by the right roles before execution.
- Change Management Impacting Financial Data: Controls governing how changes to systems or processes are authorized and tested before affecting financial outputs.
- Reconciliations and Exception Handling: Processes that compare system records to financial data to detect and correct variances.
These controls link directly to your clients’ internal control over financial reporting (ICFR) obligations, which auditors and finance teams rely on.
2. SOC 2 Trust Services Criteria Explained
SOC 2 audits evaluate controls against the five Trust Services Criteria defined by the AICPA. These criteria help provide assurance around operational risks beyond financial reporting.
Here are the SOC 2 Trust Services Criteria:
- Security (Mandatory): Ensures information and systems are protected against unauthorized access, disclosure, or damage.
- Availability: Confirms systems and services are accessible for operation and use as committed.
- Confidentiality: Ensures protection of information designated as confidential.
- Processing Integrity: Verifies processing is complete, valid, accurate, timely, and authorized.
- Privacy: Evaluates how personal information is collected, used, retained, disclosed, and disposed of according to objectives.
Knowing what controls are in scope is only half the picture; the real distinction lies in how auditors test them.
Type I vs Type II Reports: What’s the Real Difference?
Choosing between a Type I and a Type II SOC report isn’t about which is better in theory; it’s a timing and credibility decision that directly shapes how your enterprise, bank partner, or investor perceives risk.
Below is a clear side-by-side comparison to help you decide what makes sense for your business and audit strategy.
With the report type clarified, the real question becomes whether SOC 1, SOC 2, or both align with your risk exposure and stakeholders.
Does My Organization Need a SOC 1 Report, a SOC 2 Report, or Both?

When deciding whether your company should pursue a SOC 1, SOC 2, or both, there’s no one-size-fits-all answer. The right choice depends on what risks your product exposes, which stakeholders are evaluating your controls, and how your services are positioned in customer contracts and diligence processes.
Below are practical scenarios to help you align SOC reporting to your risk profile and strategic goals.
- SOC 1 is typically needed when your services impact customer financial reporting, such as payment processing, billing, settlement, or payroll platforms.
- SOC 2 is expected for SaaS, cloud, and data-driven services that handle sensitive information and must demonstrate security, availability, and processing integrity.
- Both may be required for fintech or crypto platforms that affect financial reporting and manage sensitive operational data, or for companies preparing for PE diligence or exit.
Struggling to determine which SOC report fits your business risk profile and stakeholder expectations? Fraxtional provides strategic guidance to help you scope, prepare, and align your SOC audits efficiently. Partner with us today to simplify your SOC compliance journey.
Also Read: What Is Risk and Control Self-Assessment? Framework and Execution
Now, the next challenge is reading the report without overlooking material risk.
How to Read and Interpret a SOC Report Without Missing Risk
Reading a SOC report is about scanning hidden risk signals that could affect contracts, M&A diligence, and ongoing vendor operations. While auditors issue an overall opinion, the real insights often lie in specific sections where controls didn’t perform as intended or where responsibilities are shared between you and your vendors.
Below are critical areas to focus on when you evaluate a SOC report for actual risk:
- CUECs Define Shared Responsibility: They show which controls your organization must operate for the vendor’s controls to work, such as access management or incident escalation.
- Unmet CUECs Weaken Assurance: If your controls aren’t in place, the vendor’s control results may not fully apply to you.
- CUECs Affect Audit Interpretation: Auditors use them to judge whether control objectives are actually met in a joint environment.
- Exceptions Signal Risk Patterns: Isolated failures are less concerning than repeated issues that point to systemic weaknesses.
- Management Responses Matter: Specific, timely remediation plans inspire confidence; vague explanations often indicate unresolved risk.
Now, the next step is evaluating what the final report actually tells you.
How Should Operators and Investors Evaluate SOC Reports?

Interpreting a SOC report goes well beyond seeing an “unqualified opinion.” Smart operators and investors know that what’s in the details, control design, effectiveness, exceptions, and materiality, drives real risk.
Below are the practical evaluation criteria experts use to determine where actual risk lies.
- Control Design Versus Effectiveness: Assess whether controls are appropriately designed and, for Type II reports, whether they operated effectively over time. Design alone (as in Type I) may provide initial confidence but not evidence of consistent performance.
- Coverage Versus Actual Risk Exposure: Confirm that the controls audited actually map to the areas you depend on. A lack of coverage for critical systems or sub-systems in scope can create blind spots in risk assessments.
- Exception Materiality: Not all exceptions carry equal weight. Evaluate whether exceptions could change decisions you would make, for example, those tied to financial reporting accuracy or data security, and consider their potential downstream impact.
- Alignment With Business Model and Use Cases: Ensure that the scope and control objectives in the SOC report align with how your organization actually consumes the vendor’s services.
Finding it challenging to interpret exceptions, CUECs, and audit details in SOC reports? Fraxtional helps you identify hidden risks and ensure reports align with your operational and financial priorities. Reach out to us to gain actionable insights and strengthen your audit confidence.
This is where strong compliance leadership makes the difference between surface-level review and real assurance.
How Fractional Compliance Leadership Helps Organizations Get SOC Right
When it comes to SOC compliance, what often gets overlooked is strategic leadership that ensures these efforts actually serve your business goals, buyer expectations, and investor confidence.
At Fraxtional, compliance and risk leadership focus on integrated, decision-driven guidance helping leaders make informed choices. Its approach aligns your compliance program with real risk vectors and commercial realities.
Below are key ways Fraxtional can help you get SOC compliance right:
- Scoping the Right SOC Path: Fraxtional helps you define whether SOC 1, SOC 2, or both make sense based on actual financial reporting exposure and operational risk, reducing unnecessary audit work and cost.
- Audit Readiness and Coordination: Rather than leaving you to fend for yourself, Fraxtional maps controls to audit requirements, organizes evidence, and aligns your internal processes with auditor expectations, minimizing delays and last-minute surprises.
- Stakeholder Alignment: Fraxtional ensures your SOC reports reflect what key stakeholders actually care about, whether it’s enterprise procurement, sponsor bank risk teams, or PE investors, so your narrative strengthens deal confidence.
- Control and Timeline Management: By guiding preparation and remediation, Fraxtional helps you optimize timelines and cost, preventing common slowdowns like unclear control ownership or documentation gaps.
Suggested Read: How Fractional Leadership Has Reshaped Private Equity Operations
Fraxtional’s leadership model integrates deep compliance expertise into your organization, guiding you from scoping through execution with clarity, credibility, and confidence.
Conclusion
SOC 1 and SOC 2 compliance are no longer optional artifacts you deal with at the last minute. For operators and investors, they function as decision-enabling risk tools that influence audits, enterprise deals, bank partnerships, and exit readiness.
This is where Fraxtional stands apart. Through fractional compliance leadership, Fraxtional integrates senior-level risk and compliance expertise into your organization to guide scoping decisions, prepare you for audits, align SOC reports with stakeholder expectations, and control cost and timelines, without forcing you into a full-time executive hire.
If you’re evaluating SOC readiness or unsure which report you truly need, reach out to Fraxtional to speak with a compliance leader and get a clear, risk-based path forward.
FAQs
Before you begin a SOC audit, you should have documented policies, defined systems in scope, and evidence of basic control operation. A readiness phase ensures you have clarity on scope boundaries, data flows, and control ownership so the audit isn’t derailed by documentation gaps.
SOC reports are reviewed by customer auditors, sponsor bank risk teams, enterprise procurement and vendor risk groups, PE diligence teams, and internal audit committees. Each uses them to assess control reliability, security posture, regulatory readiness, and operational risk before approving relationships or deals.
No. SOC 1 and SOC 2 are attestation reports, not certifications issued by a standards body. They reflect an auditor’s opinion on controls at a point in time or over a period; they don’t confer a compliance “badge” the way regulatory certifications do.
SOC audits range from weeks to over a year. Type I audits take 1–3 months, while Type II requires 6–12+ months due to observation periods. Timelines are driven by documentation quality, control ownership clarity, scope size, and overall internal readiness.
Vendor reviews can provide insight, but they cannot replace an independent SOC report. Best practice is to obtain SOC reports for critical vendors and integrate them into your third-party risk program as verified evidence of controls.
blogs
Don’t miss these
Let’s Get Started
Ready to Strengthen Your Compliance Program?
Take the next step towards expert compliance solutions. Connect with us today.




