Feb 13, 2026
Data Security Compliance in 2026: What Organizations Must Get Right

By Fraxtional LLC

Summarize the blog with AI
You never hear leaders say it aloud, but one of the most stressful moments in a boardroom is when an unexpected data error lands on your desk in the middle of a growth sprint. Not because someone broke a code rule, but because your business partners, investors, or banking sponsors now question whether your company truly manages its data responsibly.
The cold reality is that data security compliance is a core risk metric that can erode trust, slow deals, and even trigger expensive regulatory scrutiny. For instance, new industry research shows that in the United States, the average cost of a data breach has climbed to a record $10.22 million, even as global costs decline, driven by higher fines, compliance lapses, and governance gaps.
In this blog, we will explain what data security compliance means, why it matters for you and your investors, its core requirements, common pitfalls, best practices, relevant U.S. laws and standards, and how to implement it effectively.
Key Takeaways
- Data security compliance is a core leadership and governance responsibility that impacts regulation, investor confidence, partnerships, and overall business trust.
- U.S. compliance requirements vary by industry, data type, and growth stage, making clarity on data flows, ownership, and applicable laws essential.
- Effective programs prioritize accountability, documented controls, incident readiness, and audit-ready evidence over tools or certifications alone.
- Common failures arise from poor ownership, treating compliance as a one-time task, and not scaling programs as the business grows.
- Fraxtional provides fractional leadership that helps companies implement scalable, credible compliance programs without premature full-time hires.
Why Data Security Compliance Matters for Business Leaders Today

Data security compliance is a business reality that can make or break deals, partnerships, and trust with regulators, banks, and investors. When compliance gaps show up in due diligence, boards won’t see it as an IT problem; they’ll see it as a governance failure that reflects on leadership’s ability to manage risk and scale responsibly.
Here’s why it matters:
- Banks and sponsor partners require strong, auditable controls before underwriting fintechs or extending services, because loose data practices signal systemic risk.
- Investors treat breaches and compliance slips as governance red flags that can slow funding rounds, delay closings, or reduce valuations.
- Security incidents are now seen as leadership oversights, especially when gaps could have been prevented with strong data governance.
Also Read: How to Prepare for a PCI Audit: Expert Tips for 2026
To understand why data security compliance matters so deeply, leaders first need clarity on what it actually means.
What Data Security Compliance Actually Means
Data security compliance means you have clear policies, documented controls, and audit-ready evidence showing how your company protects sensitive data and follows laws, frameworks, and industry expectations consistently and intentionally.
Here’s how the concept breaks down for decision-makers:
- Compliance means meeting laws and rules that apply to your business and data flows, not just internal policies.
- Data security refers to practices that protect data from unauthorized access, loss, or corruption.
- Data privacy focuses on how data is used and who has rights over it, which complements but does not replace security requirements.
- Being compliant signals to regulators, banks, and investors that you have evidence of controls, governance, accountability, and ongoing oversight, not just a plan.
Now, let’s have a look at the core data security compliance requirements companies must meet.
Core Data Security Compliance Requirements Companies Must Meet
To satisfy regulators, sponsors, and institutional partners, companies must show concrete governance and controls, not promises. Here’s what leaders are expected to demonstrate at a minimum:
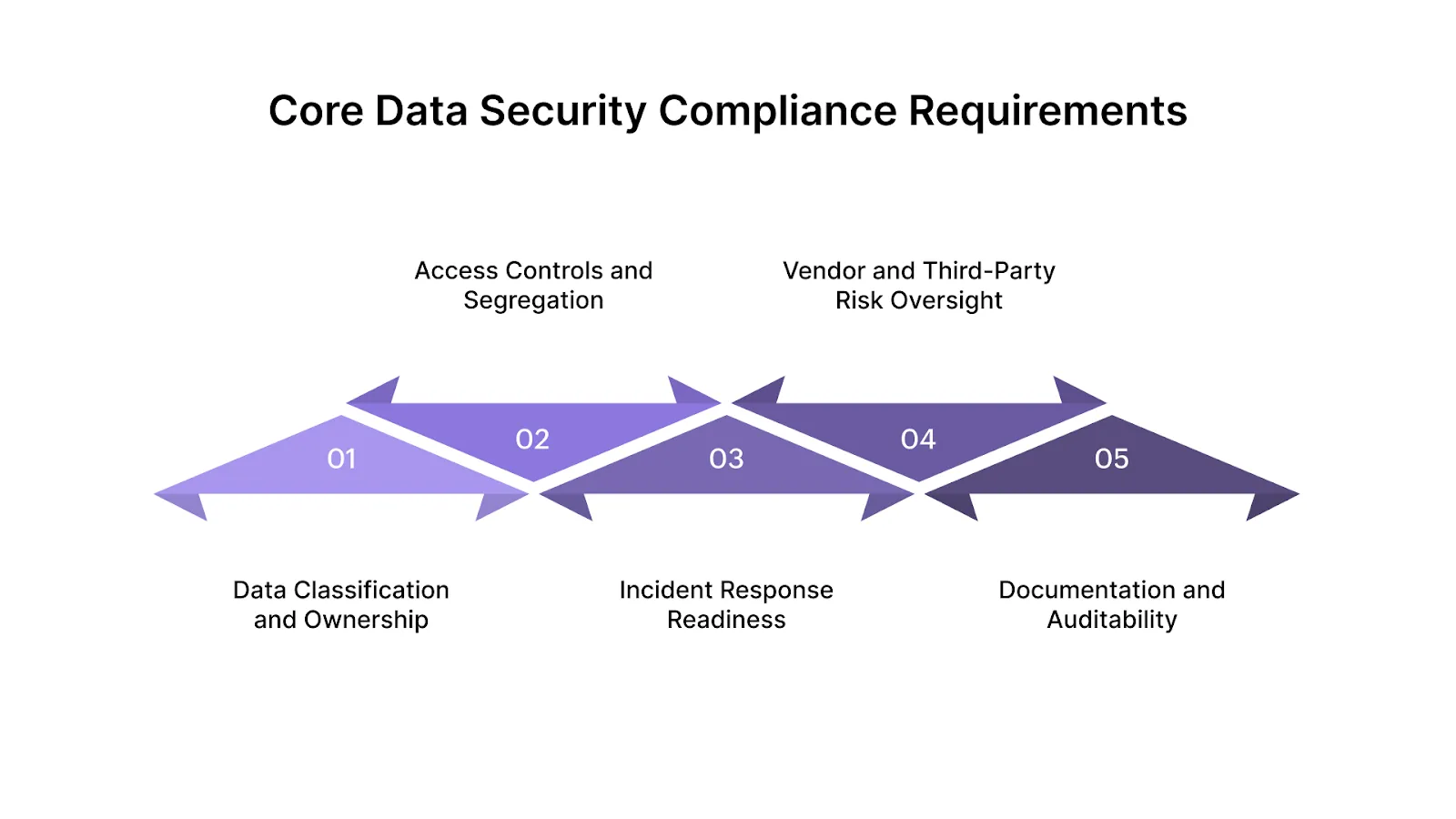
- Data Classification and Ownership: Know what data you have and how sensitive it is so you can protect the right assets at the right level. Proper classification informs risk decisions and control assignments.
- Access Controls and Segregation: Restrict access based on need-to-know and enforce segregation between roles to reduce unauthorized exposure or misuse of sensitive information.
- Incident Response Readiness: Have a documented and tested incident response plan so you can quickly contain, investigate, and report security events when they occur.
- Vendor and Third-Party Risk Oversight: Regulators and banks expect you to evaluate vendors, monitor risk over time, and adjust controls if a third party introduces new exposure.
- Documentation and Auditability: Maintain clear records of decisions, risk assessments, control evidence, and incident outcomes so auditors can trace actions back to leadership commitments.
Now, the next step is identifying which companies face the highest requirements.
Which Companies Face the Highest Data Security Compliance Requirements

Not all businesses carry the same risk or regulatory load. Some are under intense compliance pressure every day, simply because of what they do, who they partner with, or where they operate.
Here are the main categories that face the toughest requirements, and why they differ:
- Fintech and Payments Companies: Rapid innovation + sensitive financial flows = regulators and sponsor banks demanding strong controls before partnerships or deals close. These firms must prove strong AML/KYC and data governance as a baseline.
- Crypto and Digital Asset Firms: Operating across jurisdictions with changing frameworks, these companies must align with financial crime, transparency, and data safeguards, even when rules differ by state or country.
- Banks and Sponsor Banks: Traditional financial institutions are deeply regulated and must show secure, auditable reporting processes. Mid-tier banks now face heightened scrutiny on automated data integrity and reporting.
- SaaS Platforms Handling Regulated Data: Even if not a financial byproduct, SaaS firms storing or processing regulated personal or payment data must meet high security and compliance expectations as partners of banks or regulated clients.
Struggling to explain your data security posture to banks, investors, or regulators without overcommitting to a full-time hire? Fraxtional provides compliance leadership that helps you build clarity, credibility, and evidence without slowing growth. Reach out to us to explore the right next step.
With the highest-risk companies in view, the next step is understanding the U.S. data security laws that leaders should know.
Common U.S. Data Security Laws Leaders Should Know

Data security compliance in the U.S. is a patchwork of federal and state requirements that vary by industry, data type, and enforcement focus. What matters most isn’t memorizing every statute, but knowing which laws apply to your business model and where enforcement is most active.
Here’s a high-level map of the scene you need to understand:
- FTC Oversight: The FTC enforces baseline data security and privacy standards across industries, acting when companies fail to meet stated protections.
- Financial Institutions (GLBA): GLBA requires financial firms to protect nonpublic personal information through formal, documented security programs.
- Consumer Reporting Data (FCRA): FCRA regulates the collection, use, and accuracy of credit data, shaping compliance and control requirements.
- State Privacy Laws: States like California, Virginia, and Colorado impose additional privacy and security obligations for resident data.
- Sector-Specific Laws: Regulations such as COPPA and HIPAA apply targeted protections to children’s data and health information, respectively.
Also Read: Leadership in AML: Traits, Training, and Tactics for Modern Compliance Teams
Once you understand the relevant U.S. data security laws, the next step is aligning with the key compliance standards that regulated businesses follow.
Key Data Security Compliance Standards Used by Regulated Businesses
Data security compliance standards signal maturity, accountability, and commitment to risk management, without prescribing specific tools or architectures.
Here’s a clear comparison of the major standards companies commonly reference:
Now, the real work comes in implementing them step by step.
How Companies Implement Data Security Compliance: Step-by-Step
Data security compliance fails because execution is rushed, fragmented, or treated as a one-time exercise. This step-by-step approach reflects how regulators, sponsor banks, and investors actually evaluate compliance maturity.
Let’s break down what this looks like.
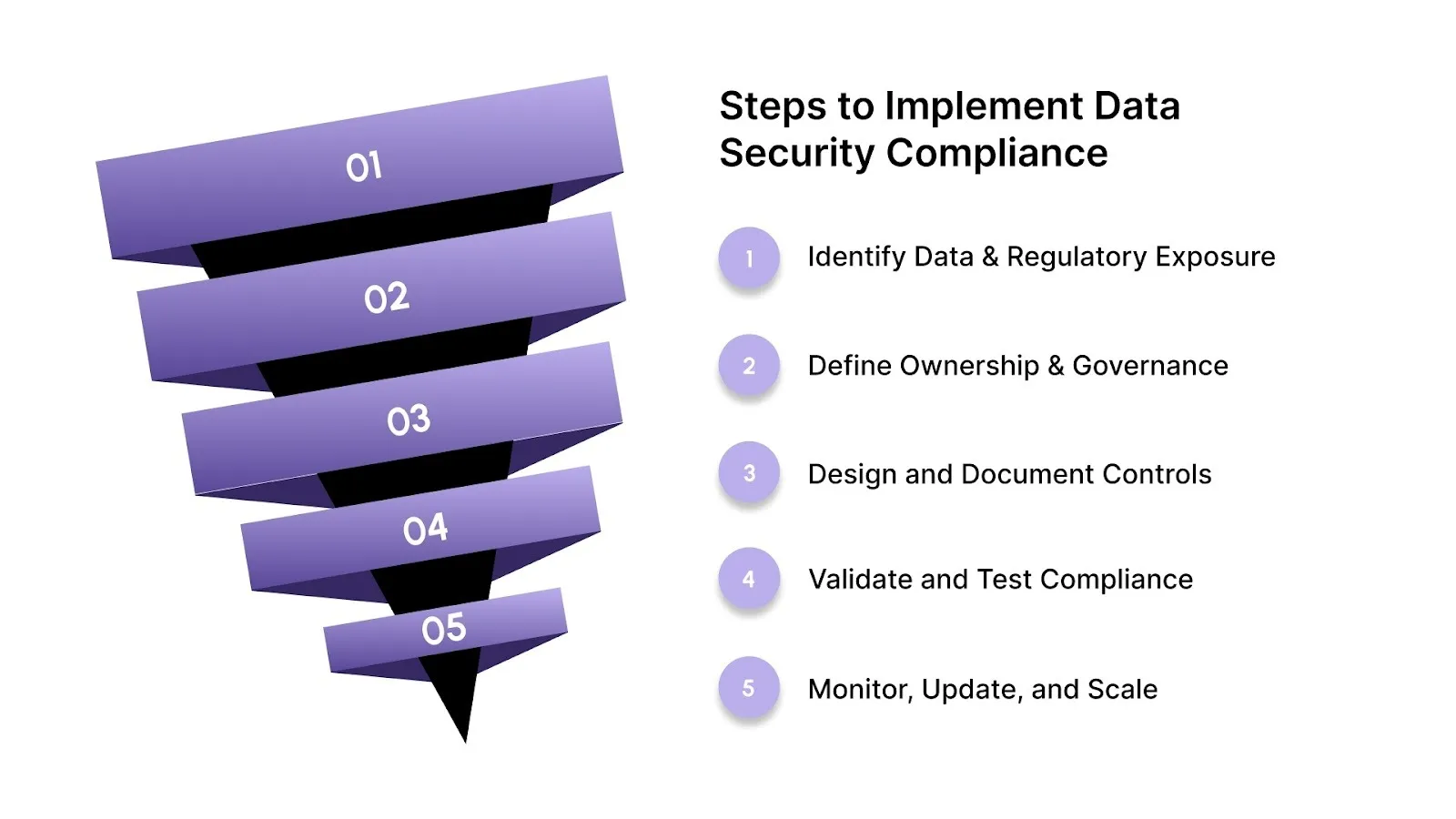
Step 1 - Identify Data and Regulatory Exposure
Before controls, audits, or certifications, strong compliance starts with clarity. Many organizations underestimate their exposure simply because they don’t fully understand what data they touch or how it flows through the business.
Key questions leaders should answer:
- What types of data do you handle? Financial data, personal data, transaction data, credentials, or proprietary business information all carry different risk levels.
- Where does this data live and move? Across products, internal systems, cloud environments, vendors, and partners.
- Which regulations apply based on that data? U.S. financial, consumer, or sector-specific rules often apply even if compliance wasn’t initially designed for them.
Step 2 - Define Ownership and Governance
Compliance breaks down quickly when “everyone owns it,” which usually means no one truly does. Regulators and banks look closely at governance because it shows whether compliance is operational or performative.
Leaders should establish:
- Named owners for data security compliance, typically at the executive or senior leadership level
- Clear decision-making authority for risk acceptance, remediation, and exceptions
- Defined escalation paths when incidents, gaps, or regulatory questions arise
Step 3 - Design and Document Controls
Controls are where strategy turns into evidence. This is not about creating thick policy binders; it’s about designing controls that actually match the business and can be explained to outsiders.
Effective controls usually include:
- Written policies that reflect how the company truly operates
- Operational procedures that teams can realistically follow
- Oversight mechanisms to ensure controls are applied consistently
Step 4 - Validate and Test Compliance
Validation is where many companies feel uncomfortable, but it’s also where credibility is built. Regulators, banks, and investors expect proof that controls don’t just exist on paper.
Common validation methods include:
- Internal reviews to confirm policies and controls are being followed
- Sample testing of access, approvals, or incident handling
- Independent assessments or audits to provide external confidence
Step 5 - Monitor, Update, and Scale
Data security compliance is a living program. As companies grow, launch new products, enter new states, or onboard new partners, risk changes, and compliance must keep pace.
Ongoing compliance requires:
- Regular reviews of data flows and vendors
- Updates to controls as business models change
- Continuous oversight and reporting to leadership
Also Read: Leadership in FinTech Innovation: 7 Trends Redefining the Industry
After outlining the implementation steps, it’s important to consider the different compliance approaches organizations adopt.
Types of Data Security Compliance Approaches Companies Take
Every company’s compliance journey looks different because risk, partners, regulations, and growth trajectories aren’t the same. Some firms aim for minimal coverage, others build strong, multi-jurisdictional programs, and a few pursue compliance strategies driven by investors or banking partners.
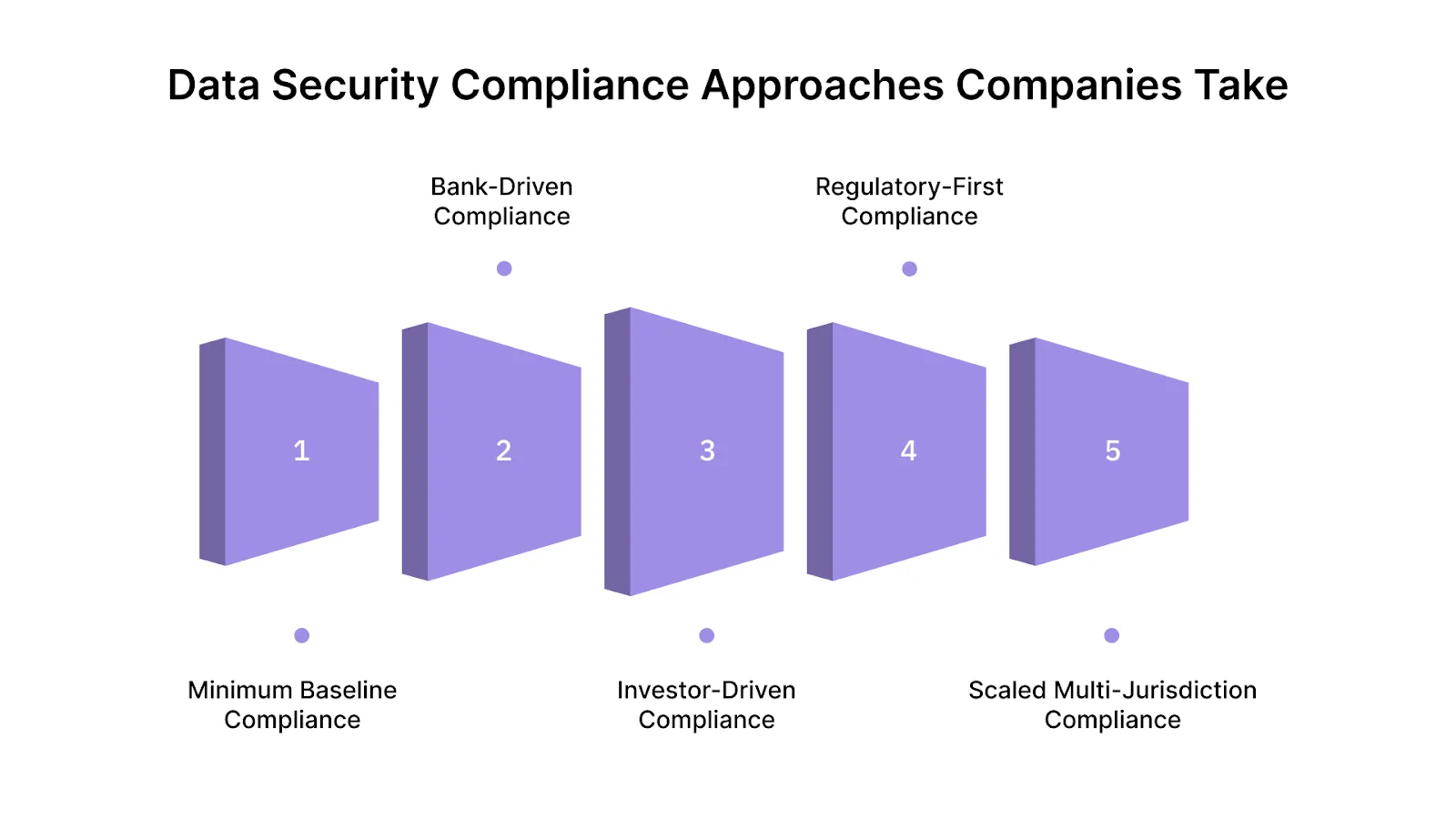
Here’s the breakdown:
- Minimum Baseline Compliance: Focuses on core requirements to stay legal and avoid obvious gaps. Fast and cheap to start, but it often leaves latent risks identified as products, customers, or markets expand. It’s a foundation, not a finish line.
- Bank-Driven Compliance: Tailored to the expectations of sponsor banks, including stronger documentation, audit trails, and evidence-ready controls. This approach slows implementation slightly and costs more, but it reduces partner risk exposure and accelerates institutional deals.
- Investor-Driven Compliance: Investors increasingly require evidence of risk governance before putting capital down. Programs built to satisfy investor due diligence tend to be stronger than minimum compliance and balance cost with strategic risk reduction.
- Regulatory-First Compliance: Designed around meeting or exceeding laws and standards that matter to regulators. This takes longer and demands more investment, but it minimizes regulatory risk, which is often the hardest risk to recover from.
- Scaled Multi-Jurisdiction Compliance: For companies operating across states or countries, compliance needs to cover multiple regulatory regimes simultaneously. This is the most expensive and slowest to implement, but crucial for global expansion and seamless cross-border operations.
Also Read: Why Banks Are Replacing Full-Time Executives With Fractional Leaders in 2025
Now, let’s see some common data security compliance mistakes to avoid.
Most Common Data Security Compliance Mistakes Companies Make

Many compliance failures aren’t technical; they’re leadership and execution missteps. Decision-makers often don’t notice these until they surface in audits, partner reviews, or regulatory assessments.
Here are the most frequent mistakes and practical fixes that reduce risk:
- Treating Compliance as a One-Time Project: Many teams rush to “check the box” once and move on. Compliance is ongoing; threats, partners, and regulations change.
- Fix: Build a recurring review cycle tied to product launches, market expansions, and quarterly leadership check-ins.
- Assigning Ownership Too Low in The Org: When compliance is driven only by mid-level IT, it lacks strategic direction and accountability across risk, product, and legal.
- Fix: Give executive ownership (e.g., CRO/GC/CISO level) with clear escalation paths to the CEO and board.
- Over-Relying on Vendors or Tools: Buying security products isn’t the same as managing risk. Tools help, but they don’t replace policy, governance, or evidence.
- Fix: Align vendor outputs with documented controls and business rules, and verify them regularly.
- Ignoring sponsor bank expectations: Banks and financial partners often have specific evidence, reporting, and control expectations that differ from generic checklists.
- Fix: Align your compliance program with key partners’ checklists early and integrate sponsor feedback into your roadmap.
If your compliance program feels reactive, fragmented, or overly tool-driven, you are not alone. Fraxtional helps companies replace patchwork fixes with experienced, fractional leadership that scales with real risk. Contact us to partner on a smarter compliance approach.
Now, let’s look at practical examples of how companies implement data security compliance effectively.
Practical Examples of Data Security Compliance in Action

These brief, practical scenarios show how compliance decisions play out in business contexts, and why outcomes matter for growth, partners, and regulators.
- Fintech is Preparing for Sponsor Bank Onboarding: A U.S. fintech aiming to partner with a sponsor bank aligned its controls, documentation, and audit evidence to the bank’s AML and data governance expectations early in the process.
- Crypto Firm Expanding Across U.S. States: As a crypto trading and custody platform expanded into additional states, it mapped its customer-data processes against multiple regulatory frameworks and built a uniform compliance evidence repository.
- Private Equity Firm Assessing Portfolio Compliance Risk: A PE investor evaluating a portfolio company’s security posture discovered gaps in vendor risk oversight and documentation.
- Bank Strengthening Fintech Partnership Controls: A mid-tier bank revised its third-party risk evaluations after noticing inconsistent data security practices among fintech partners.
These examples show how effective execution looks, and why experienced Fraxtional leadership can make compliance both achievable and strategic.
Why Fraxtional Leadership Is Effective for Data Security Compliance

When data security compliance is critical, hiring your first full-time C-suite executive often happens too early; before the business has a clear scope, partners, or regulatory certainty.
That’s where Fraxtional’s tailored leadership model steps in. Fraxtional helps you build, operationalize, and sustain compliance programs without the cost or commitment of a full-time hire.
Here’s why this model works especially well for founders, compliance leaders, banks, crypto firms, and private equity investors:
- Full-Time Hires are Often Premature: Early hires at executive salary levels can strain budgets and slow momentum. Fraxtional gives you senior compliance leadership on demand, aligned with your growth stage and regulatory pressure points.
- Experienced Leadership Reduces Regulatory Friction: Fraxtional directors bring decades of practical experience working with regulators, sponsor banks, and audit partners, turning compliance from uncertainty into evidence-ready confidence.
- Fractional Roles add Value Where it Matters Most: Whether it’s policy development, audit readiness, SOC 2 alignment, money transmitter licensing, or sponsor bank engagements, Fraxtional’s leadership integrates seamlessly into your operations and accelerates outcomes.
- Transition to Internal Ownership When the Time is Right: As your compliance maturity grows and internal teams strengthen, Fraxtional supports the transition toward in-house leadership with continuity and knowledge transfer.
Fraxtional bridges the gap between early ambition and compliance-ready execution, giving you strategic oversight, operational discipline, and confidence that your data security compliance program is resilient, scalable, and business-aligned.
Also Read: The Rise of Fractional C-Suite Executives in Crypto
Final Thoughts
Data security compliance has become a core leadership responsibility, not a background technical task. For founders, executives, and investors, getting it right protects enterprise value, accelerates partnerships, and reduces regulatory friction as your business scales.
This is where Fraxtional adds outsized value. Fraxtional provides experienced, C-suite risk and compliance leadership that helps fintechs, banks, crypto firms, and private equity-backed companies design, execute, and scale data security compliance programs without premature full-time hires.
If you want clarity on your current compliance posture or guidance on building a scalable data security compliance program, reach out to Fraxtional to speak with a senior compliance leader and understand the right next step for your business.
FAQs
Legal responsibility ultimately sits with company leadership, not IT teams. Regulators and courts expect executives and boards to ensure appropriate oversight, risk governance, and accountability structures.
Yes. Even early-stage startups are subject to data security obligations if they handle financial, personal, or regulated data. While expectations scale with size and risk, regulators, banks, and investors increasingly assess compliance maturity early.
At a minimum, programs should be reviewed annually. Reviews should also occur after major events such as new product launches, market expansion, regulatory changes, significant vendor onboarding, or security incidents.
No. Cybersecurity focuses on protecting systems and data from threats, while data security compliance focuses on meeting legal, regulatory, and governance expectations. Strong cybersecurity supports compliance, but compliance additionally requires documentation, accountability, and alignment with laws and partner requirements.
Yes. Certifications help demonstrate maturity, but they are not legally required in most cases. Regulators and banks care more about effective controls, governance, and evidence.
blogs
Don’t miss these
Let’s Get Started
Ready to Strengthen Your Compliance Program?
Take the next step towards expert compliance solutions. Connect with us today.




